Leveraging Copilot In Excel To Steal Data Without Any User Interaction
I Don’t Want My, I Don’t Want My, I Don’t Want My AI PC
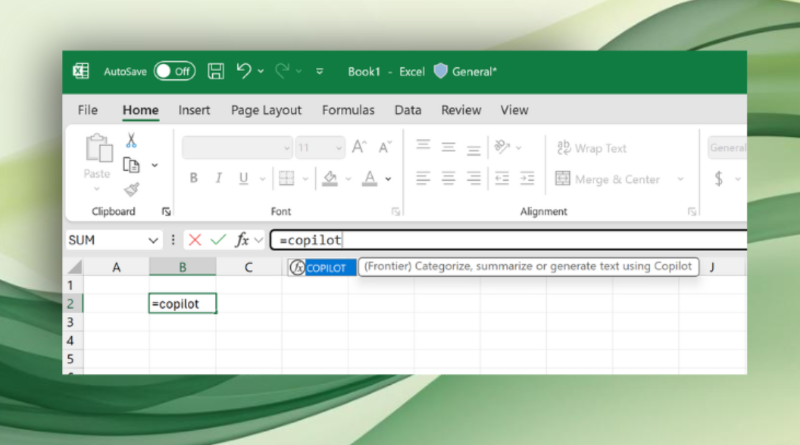
Patch Tuesday has come and gone once more and this time it contained a doozy of a patch, not that it was communicated willingly to customers. This has become standard practice at Microsoft, as they no longer make it easy to get hold of the details of what exactly they were patching. Thankfully The Register had the time to track down the relevant KB and they discovered that among the 83 Microsoft CVEs was one that should terrify any business which hasn’t been able to keep Microsoft’s Copilot out of their user’s Excel.
This is a cross-site scripting flaw, one that could likely be leveraged via a modified SharePoint or Teams link, could be used to cause Copilot Agent mode to exfiltrate data from whatever Excel documents you have open. While you can use Excel for cross stitch patterns, it is far more likely your Excel document contains proprietary data. If you happen to fall victim to this attack, Copilot will happily save that worksheet somewhere you really don’t want that data to end up.
This vulnerability and others are discussed in a bit more detail at The Register, but even following the links won’t explain exactly how Copilot can be convinced to leak your data in new and interesting ways,