Microsoft adds Windows protections for malicious Remote Desktop files
Microsoft has introduced new Windows protections to defend against phishing attacks that abuse Remote Desktop connection (.rdp) files, adding warnings and disabling risky shared resources by default.
RDP files are commonly used in enterprise environments to connect to remote systems because admins can preconfigure them to automatically redirect local resources to the remote host.
Threat actors have increasingly abused this functionality in phishing campaigns. The Russian state-sponsored APT29 hacking group has previously used rogue RDP files to remotely steal data and credentials from victims.
When opened, these files can connect to attacker-controlled systems and redirect local drives to the connected device, allowing the attacker-controlled device to steal files and credentials stored on disk.
They can also capture clipboard data, such as passwords or sensitive text, or redirect authentication mechanisms like smart cards or Windows Hello to impersonate users
New RDP protections roll out
As part of the April 2026 cumulative updates for Windows 10 (KB5082200) and Windows 11 (KB5083769 and KB5082052), Microsoft has now released new protections to prevent malicious RDP connection files from being used on devices.
“Malicious actors misuse this capability by sending RDP files through phishing emails,” warns Microsoft.
“When a victim opens the file, their device silently connects to a server controlled by the attacker and shares local resources, giving the attacker access to files, credentials, and more.”
After installing this update, when users open an RDP file for the first time, a one-time educational prompt is shown that explains what RDP files are and warns about their risks. Windows users will then be prompted to acknowledge that they understand the risks and press OK, which will prevent the alert from being shown again.
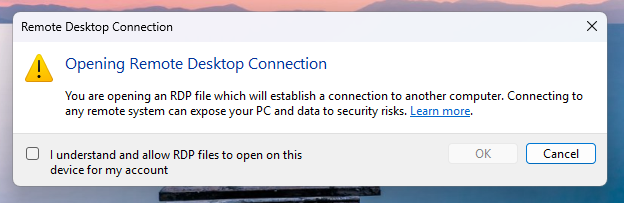
Source: Microsoft
Future attempts to open RDP files will now display a security dialog before any connection is made.
This dialog shows whether the RDP file is signed by a verified publisher, the remote system’s address, and lists all local resource redirections, such as drives, clipboard, or devices, with every option disabled by default.
If a file is not digitally signed, Windows displays a “Caution: Unknown remote connection” warning and labels the publisher as unknown, indicating there is no way to verify who created the file.
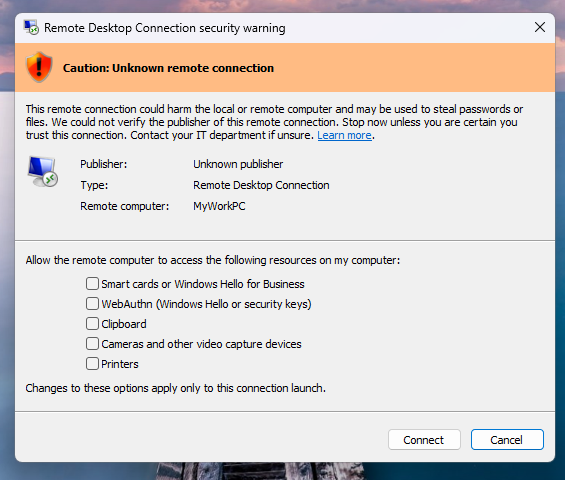
Source: Microsoft
If the RDP file is digitally signed, Windows will display the publisher, but still warn you to verify their legitimacy before connecting.
It should be noted that these new protections apply only to connections initiated by opening RDP files, not to those made through the Windows Remote Desktop client.
Microsoft says that Administrators can temporarily disable these protections by going to the HKLM\Software\Policies\Microsoft\Windows NT\Terminal Services\Client Registry key and modifying the RedirectionWarningDialogVersion value so it is set to 1.
However, as RDP files have historically been abused in attacks, it is strongly recommended to keep these protections enabled.






